All of my code can be viewed on my Github: https://github.com/chaintuts
Featured Content
Code
All of my code can be viewed on my Github: https://github.com/chaintuts
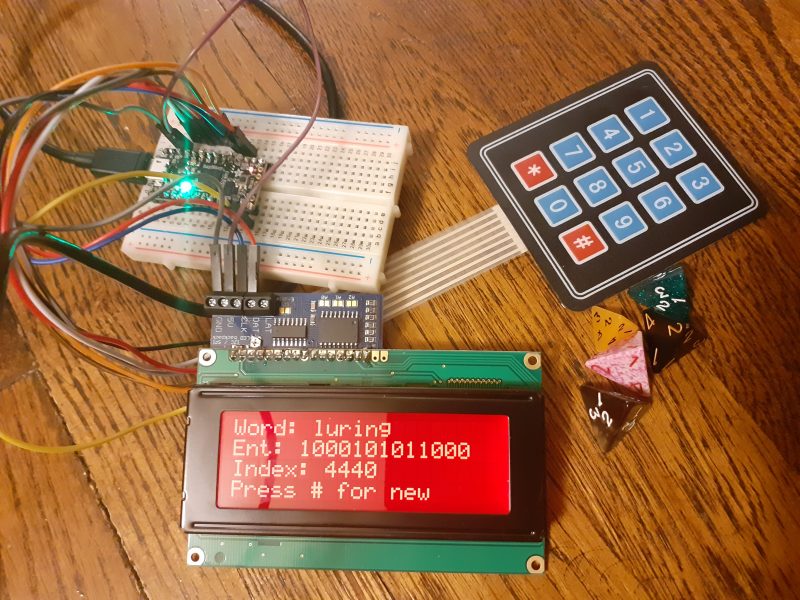
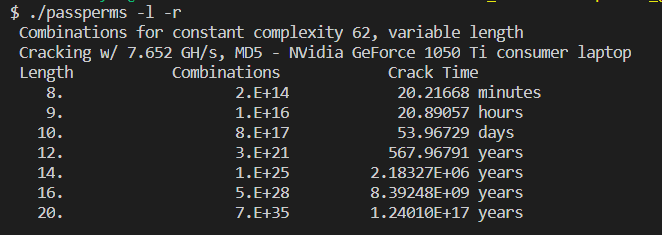
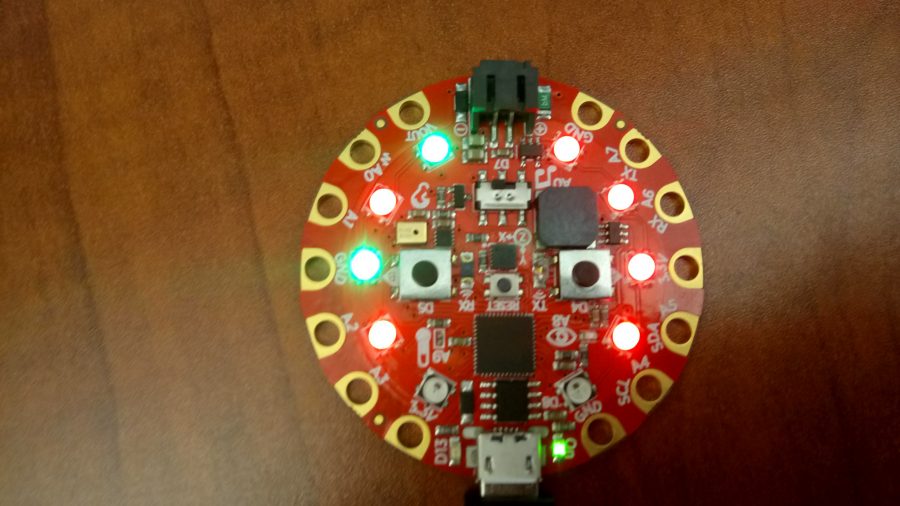
Many code projects with different technologies, covering everything from cryptocurrencies to cybersecurity to hobby interests and more!
This code: see repositories for detailed licenses. All projects use the BSD 2-clause License.Sharing and reuse (with attribution) is highly encouraged!
Videos
All videos are available under the CC-BY 4.0 license.Sharing and reuse (with attribution) is highly encouraged!
chaintuts Tech Education
My chaintuts Youtube channel link
Josh’s Active Adventures
My Josh’s Active Adventures channel link
Photos
All of my photos can be viewed on my Flickr page: https://flickr.com/joshmcintyre
All photos are available under the CC-BY 4.0 license.Sharing and reuse (with attribution) is highly encouraged!